Cyber Security
5 Hours 30 mins
19 Students
53 Lessons
English

14 Structured Modules (Basics to Advanced)
Fully Lab-Based Training (Kali Linux Environment)
Real Attack Lifecycle Methodology
SQL Injection & XSS Practical
Advanced Nmap & CVE Mapping
Metasploit Framework Practice
Privilege Escalation Concepts
Reporting & Bug Bounty Guidance
The Ethical Hacking Master Course is a complete, lab-driven program designed to take learners from foundational cybersecurity knowledge to advanced penetration testing methodology.
The course begins with ethical hacking principles, legal boundaries, and lab architecture setup using Kali Linux and vulnerable environments. It then progresses into networking deep dives, reconnaissance, enumeration, vulnerability discovery, and web exploitation.
Advanced modules cover password attacks, Metasploit exploitation, privilege escalation, post-exploitation awareness, defensive thinking, professional reporting, and bug bounty career pathways — all within a safe and controlled virtual lab environment.
For Assignments and Projects Please go through this Link: Ethical Hacking Mastery Course

Mentor Name: Aayush:
With 4+ years of experience in Cyber Security and Ethical Hacking, I have trained students, developers, and IT professionals to understand real-world cyber threats and how to defend against them effectively.
My training focuses on practical, hands-on learning, where students work with real tools and techniques used by security professionals to identify vulnerabilities and secure systems.
Key Expertise:
• 4+ Years of Training Experience in Ethical Hacking, Network Security, and Web Application Security.
• Hands-on experience with industry tools such as Kali Linux, Metasploit, Nmap, Wireshark, and Burp Suite.
• Teaching penetration testing, vulnerability assessment, and system security techniques used by professionals.
• Specialized in Web Security, including vulnerabilities like SQL Injection, Cross-Site Scripting (XSS), authentication flaws, and misconfigurations.
• Designed real-world labs and attack simulations to ensure students gain practical experience.
• Mentored hundreds of students in starting careers in Cyber Security, Bug Bounty, and Security Research.
Training Approach
The goal of this training is to help learners think like a hacker to secure systems like a professional, combining strong fundamentals with real-world cyber security practices.
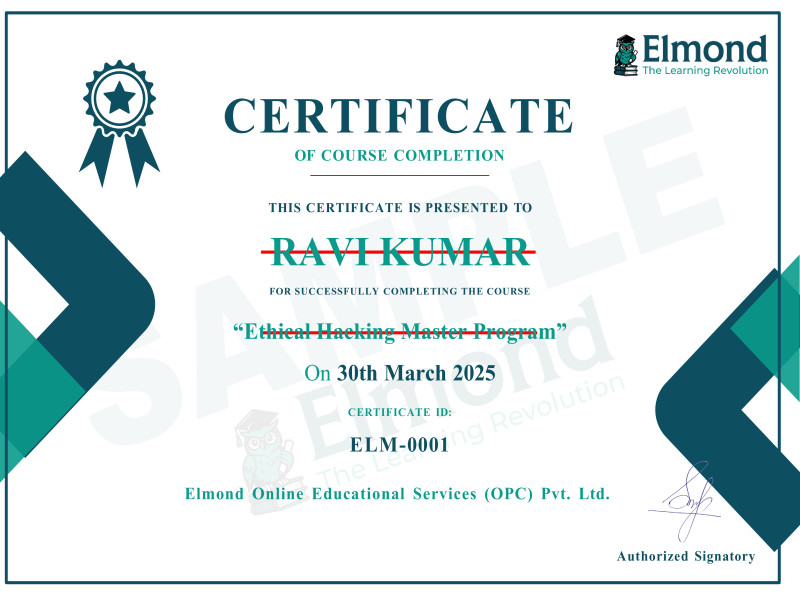
After completing the Ethical Hacking Master Course, you will receive an official Course Completion Certificate validating your practical penetration testing knowledge.
This certificate demonstrates your understanding of:
• Reconnaissance & Scanning
• Vulnerability Assessment
• Web Exploitation Basics
• Metasploit Framework Usage
• Privilege Escalation Concepts
• Professional Reporting
You can showcase it on your resume, LinkedIn profile, or cybersecurity portfolio.